The articles I wrote about the FRITZ!Box are pretty popular. They are creating the most traffic on my website. I understand this, cause the FRITZ!Box is a really great piece of hardware and AVM is also a company which knows how to make their users happy by serving regular updates to the firmware. Although I didn’t tuned my FRITZ!Box any further, I updated it with the latest Labor firmware version regularly. At some point the sshd setup (with dropbear) doesn’t worked anymore and I decided it is the time to update my software as well. Beside that it didn’t work anymore it is always a good idea to update software which allow access to a host from everywhere very regularly. Anyway, it turned out this isn’t as simple as I initial thought. Therefore here is the next post in the FRITZ!Box tuning series, which shows how to cross-build software for the MIPS32 architecture used in the FRITZ!Box and in particular get the sshd software to life again. I use a FRITZ!Box Fon WLAN 7270 v2 and the firmware is 54.05.05. Please make sure you read the other FRITZ!Box articles as well, cause some of the information given there still applies.
As already mentioned in the other articles, there is no warranty that this will work on your side and I am not responsible for any damage which may happen. You have been warned!Cross-building for the MIPS32 architecture
The FRITZ!Box itself doesn’t include any build tools. Why should it! It’s an end-consumer product which is usually never changed, beside the user is updating it with an official firmware update. So we have to do it ourself. Creating a build chain for another architecture is usually hard. There are several things you have to consider. This includes problems with the configuration, endianess differences between the host and the target, bit depths and depending shared libraries which have to be available in the target format. Fortunately this is a common problem, especially for embedded systems, which means there is a proper solution called Buildroot (look at the first line in dmsg, when the FRITZ!Box has booted and you know what I mean). Buildroot is a build system which allows, similar to the Linux kernel, configuring and generating complete embedded Linux systems. Regardless how configured, Buildroot builds a complete Linux system, always. This is of course a little bit overhead for us, but we just pick out the relevant files. First we need to know which architecture we target. You have to login into the FRITZ!Box either using telnet or a working ssh daemon. To get some information about the hardware used in your FRITZ!Box execute cat /proc/cpuinfo.
# cat /proc/cpuinfo system type : TI UR8 (7270) processor : 0 cpu model : MIPS 4KEc V6.8 BogoMIPS : 359.62 wait instruction : yes microsecond timers : yes tlb_entries : 16 extra interrupt vector : yes hardware watchpoint : no ASEs implemented : shadow register sets : 1 core : 0 VCED exceptions : not available VCEI exceptions : not available
Here we learn that the FRITZ!Box is using a MIPS processor. In this case it uses the little-endian format. Next you need some information about the system C library. On normal Linux (desktop) systems the GNU C Library is used. This library is heavyweight and therefore the uClibc was invented for embedded systems. By executing ls /lib/libuClibc* you get the version installed. In my case it is 0.9.31. Now we have all information needed to configure Buildroot. Download and extract the source of Buildroot.
By executing make menuconfig in the root directory of Buildroot you are able to configure it. The most important options are Target Architecture, set this to mipsel and Target Architecture Variant, set this to mips 32r2. In Toolchain -> uClibc C library Version select a version which is close to the one on your FRITZ!Box. Next you have to select which packages should be build in Package Selection for the target. Choose whatever you want but for the beginning Networking applications -> openssh might be enough. If you prefer a more lightweight ssh implementation dropbear may also an option. In the following we use OpenSSH. You can also tweak the build options, like the gcc version to use or set the gcc optimization level to -O3 in favor of size. After saving the configuration and executing make, it is time for a coffee. When the build has been finished all relevant files are in output/target/. We only pack the directories and files which are necessary. For example the libuClibc was built by Buildroot, but we will use the one from the FRITZ!Box. The following create a zip archive of the files for OpenSSH.
zip -r ../../local.zip "lib/libutil* lib/libnsl* lib/libresolv* lib/libcrypt* usr/lib usr/share usr/sbin usr/bin etc/ssh_config etc/sshd_config"
Creating overlay directories on the root filesystem
The following is based on ideas invented by the guys at http://www.spblinux.de/. Our aim is it to have as little persistent changes on the FRITZ!Box as possible. This allows us to go back to the original state with a simple reboot. Therefore all writeable directories will be on a tmpfs filesystem. tmpfs filesystems are created in RAM and the content will be removed when the filesystem is unmounted. Because the FRITZ!Box has only limited RAM, we will not copy our applications into the tmpfs filesystem, but just create symbolic links to the files on the USB stick (where usually much more space is available). Because we want the applications from the FRITZ!Box and our own one be accessible from the root filesystem, we need to merge both into the tmpfs directory. Therefore first symbolic links into the original filesystem and second symbolic links to the USB stick are created. The second step is only performed when there isn’t a file already. This makes sure the original files are always preferred over our own one. The last step is binding the directories to the root filesystem. Summarized the following will be done:
- remount
/readonly - mount
/into/var/_ro_ - create tmpfs in
/var/_overlay_ - symlink the files from
/var/_ro_into/var/_overlay_ - symlink the files from the USB stick into
/var/_overlay_ - bind the directories in
/var/_overlay_to/
This script does the previous steps. It uses helper methods which are defined in common.sh. You will find all the necessary files in the package you can download at the end of this article.
#!/bin/sh . common.sh MNT=/var/_overlay_ BASE_RO=/var/_ro_ BASE_OVL="${BASE}/local" DIRS="lib etc usr/bin usr/sbin usr/lib usr/share" # remount root readonly "${MOUNT}" | "${GREP}" "/dev/root" | "${GREP}" -q ro [ $? -eq 1 ] && _lmt /dev/root / "-o remount -r" # bind root into var _lchkmnt "${BASE_RO}" if [ $? -eq 1 ]; then _lmkdir "${BASE_RO}" _lmnt / "${BASE_RO}" "-o bind" fi # create our overlay dir _lchkmnt "${MNT}" if [ $? -eq 1 ]; then _lmkdir "${MNT}" _lmnt tmpfs "${MNT}" "-t tmpfs" fi # link/copy the base stuff for i in ${DIRS}; do _lsymlnk_dir "${BASE_RO}" "${i}" "${MNT}" done # link/copy our own stuff for i in ${DIRS}; do _lsymlnk_dir "${BASE_OVL}" "${i}" "${MNT}" done # now bind all overlay dirs to root # (this is critical don't interupt) for i in ${DIRS}; do _lmnt "${MNT}/${i}" "/${i}" "-o bind" done exit 0
Now copy the zip archive you have created above to the FRITZ!Box and unpack it on the USB stick in addons/local/. The scripts have to be placed into addons/. You need to configure the following in common.sh:
# the base of the usb stick goes here: BASE="/var/media/ftp/FLASH-DISK-01/addons" # add the encrypted root password here: PASS=""
Point to the base directory within the USB stick in BASE. Also add your encrypted root password into PASS. This will create a root user in /etc/passwd automatically.
If you believe all is correct, you can start the installation by executing ./install.sh. If no errors are shown, you can try ssh. ssh -v should output something like this:
# ssh -v OpenSSH_5.8p2, OpenSSL 1.0.0d 8 Feb 2011 ...
Additional to the standard filesystems mounted, you should see the following when executing mount:
# mount ... /dev/root on /var/_ro_ type squashfs (ro,relatime) tmpfs on /var/_overlay_ type tmpfs (rw,relatime) tmpfs on /lib type tmpfs (rw,relatime) tmpfs on /etc type tmpfs (rw,relatime) tmpfs on /usr/bin type tmpfs (rw,relatime) tmpfs on /usr/sbin type tmpfs (rw,relatime) tmpfs on /usr/lib type tmpfs (rw,relatime) tmpfs on /usr/share type tmpfs (rw,relatime)
Configure and start the OpenSSH daemon
Now that we have our brand new OpenSSH on the FRITZ!Box working, we need some last steps to let the daemon running correctly. First create a private/public RSA host key pair for the server process by executing:
ssh-keygen -t rsa -f addons/config/ssh_host_rsa_key
addons/config/ have to be an existing directory below the USB stick base. Next create a file addons/config/sshd_config in the same directory with the following content:
Protocol 2 UsePrivilegeSeparation no Subsystem sftp /usr/lib/sftp-server
The following script could be use to start the sshd:
#!/bin/sh . common.sh SSHD="/usr/sbin/sshd" SSH_SPKEY="${BASE}/config/ssh_host_rsa_key" SSH_CFG="${BASE}/config/sshd_config" SSH_TPKEY="/var/tmp/ssh_host_rsa_key" # sanity check [ ! -e "${SSHD}" ] && _lce $? "sshd not installed" # start in tmp cd /var/tmp mount -o remount devpts /dev/pts -t devpts # cp key and make them user readable only _lcp_file "${SSH_SPKEY}" "${SSH_TPKEY}" _lchmod 400 "${SSH_TPKEY}" # start sshd "${SSHD}" -f "${SSH_CFG}" -h "${SSH_TPKEY}"
Please note that you have to set up the root user first and maybe adjust your port forwarding rules to allow access from the Internet as described in this post. The package will contain a script startup.sh which will add the root user automatically.
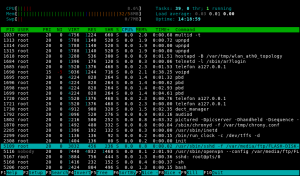
Here is the obligatory screenshot which shows htop with color terminal support. You see OpenSSH and OpenVPN in the list of the running processes.
Conclusion
Thanks to Buildroot it is pretty easy to cross-build for embedded machines these days. With some tricky directory rebinding new applications could be injected into the FRITZ!Box root filesystem without overwriting the existing firmware. Now you should be able to build any software already bundled with Buildroot or even add new one to the build process. Happy cross-building!
You can download the scripts and binaries discussed in this post:FRITZBox_OpenSSH_5.8p2.tar.gz (3.8MB, SHA1)